HIPAA: Yoga teachers’ responsibilities concerning private student information

About ten years ago, I ran a wellness center that housed different types of practitioners, including yoga teachers, massage therapists, acupuncturists, and movement therapists. One day a laptop belonging to an acupuncturist was stolen from the center. She was away from the practitioner’s office, attending to her client in the treatment room for maybe 15 minutes. Apparently, that was enough time for someone to reach the second floor of the center through three sets of unlocked doors, grab her laptop, and leave. None of us could have ever imagined that it would happen in broad daylight in our place of business, yet it did.
The aftermath of the theft was stressful. Not only did the acupuncturist lose her laptop and had to replace it, but she also lost her clients’ records, which weren’t saved elsewhere, and she potentially exposed sensitive health information. She had to notify each client about the theft, file an incident report, immediately change all of her passwords, and more. Losing one’s computer is bad enough, but it becomes much worse if that computer contains sensitive health information belonging to others.
As a yoga teacher, you might believe that a theft like that would never happen to you or that the information you keep about your students is not even sensitive. However, according to the Health Insurance Portability and Accountability Act (HIPAA), which became law in the US in 1996, Protected Health Information (PHI) is defined as “any individually identifiable health information relating to the past, present or future health condition of the individual regardless of the form in which it is maintained (electronic, paper, oral format, etc.).”
PHI includes any health-related information that you receive or create during your work with your student if it contains individually identifiable information, such as a name, an address, an email address, a medical record number, an IP address, facial photographs, or any other unique identifiers or codes. For example, if your student emails you a lab report, a physical therapy exercise sheet, or a doctor’s recommendation, and the document contains a name, email address, or other identifiable information, it is PHI, and you are responsible for keeping it safe. Moreover, any notes you make in the process of working with your student, whether paper or electronic, which identify your client in some way, are considered PHI. And HIPAA protects any data considered to be PHI.
According to the HIPAA, as a yoga teacher or therapist, you are a Covered Entity, which means that you are in a direct relationship with the individuals whose PHI you retain. As a Covered Entity, you bear certain responsibilities under the law that fall under two main categories: the HIPAA Privacy Rule and the HIPAA Security Rule. The HIPAA Privacy Rule focuses on the protection of all PHI from a people standpoint, and the HIPAA Security Rule establishes minimum safeguards for electronic PHI in terms of technology standards.
Under the HIPAA Privacy Rule, as a yoga teacher or yoga therapist, you are required to do the following:
- Avoid sharing private client information with anyone, even in casual or educational environments, unless it is necessary for running your practice.
- If you have to share a client’s PHI as a necessary part of running your practice, you need to take two precautions:
- Share the minimum amount of information necessary to perform the task.
- Ensure that the businesses or people you share this information with (accountants, scheduling services, recordkeeping services, email/hosting companies, marketing services, IT firms, etc.) are HIPAA compliant.
- Never leave private records lying around; keep paper records locked in a cabinet and electronic records stored under password protection.
- Always log out of websites and accounts before leaving your computer unattended.
- Use a secure email service when sharing PHI.
- Keep PHI records for at least six years.
- Dispose of unnecessary records properly (shredding paper records and erasing electronic records completely).
- Notify clients about the improper use or disclosure of records.
- Make all records available to clients upon request.
Under the HIPAA Security Rule, as a yoga teacher or therapist, you are required to set up the following safeguards to protect PHI:
- Administrative safeguards: Contingency plans for emergencies (floods, fires, theft, etc.) and procedures for reporting security incidents to clients
- Physical safeguards: Door locks and cabinet locks to protect paper records and computers, and data backups stored off-site
- Technical safeguards: Encrypted computer hard drives (not required but recommended), usernames, and passwords, firewalls, and other access controls that discourage hackers and protect information from malware and viruses
In addition, as a yoga teacher or therapist, you need to do the following:
- Provide all students with a HIPAA notice of privacy practices (and follow the responsibilities outlined in that document).
- Store and transmit records securely (following the physical and electronic security requirements outlined above).
- De-identify records by removing any identifiable information when using them as case studies or teaching examples.
- Have action protocols for potential security breaches.
- Ensure that organizations you use to manage students’ data are HIPAA-compliant and sign a Business Associate Agreement with each organization.
- (Recommended) Take HIPAA awareness training to better understand the intricacies of the law.
These measures might seem overwhelming, but in reality, they are common sense and are already implemented in other industries. All of our students should trust that whatever information they share with us is handled carefully and stored securely. It is always better to be prepared than to be caught off guard.
It is the personal responsibility of every yoga teacher and therapist to be HIPAA compliant, and each one of us needs to take steps to ensure it.
Electronic Health Records usually contain the medical and treatment history of a patient along with a broader view of patient care.
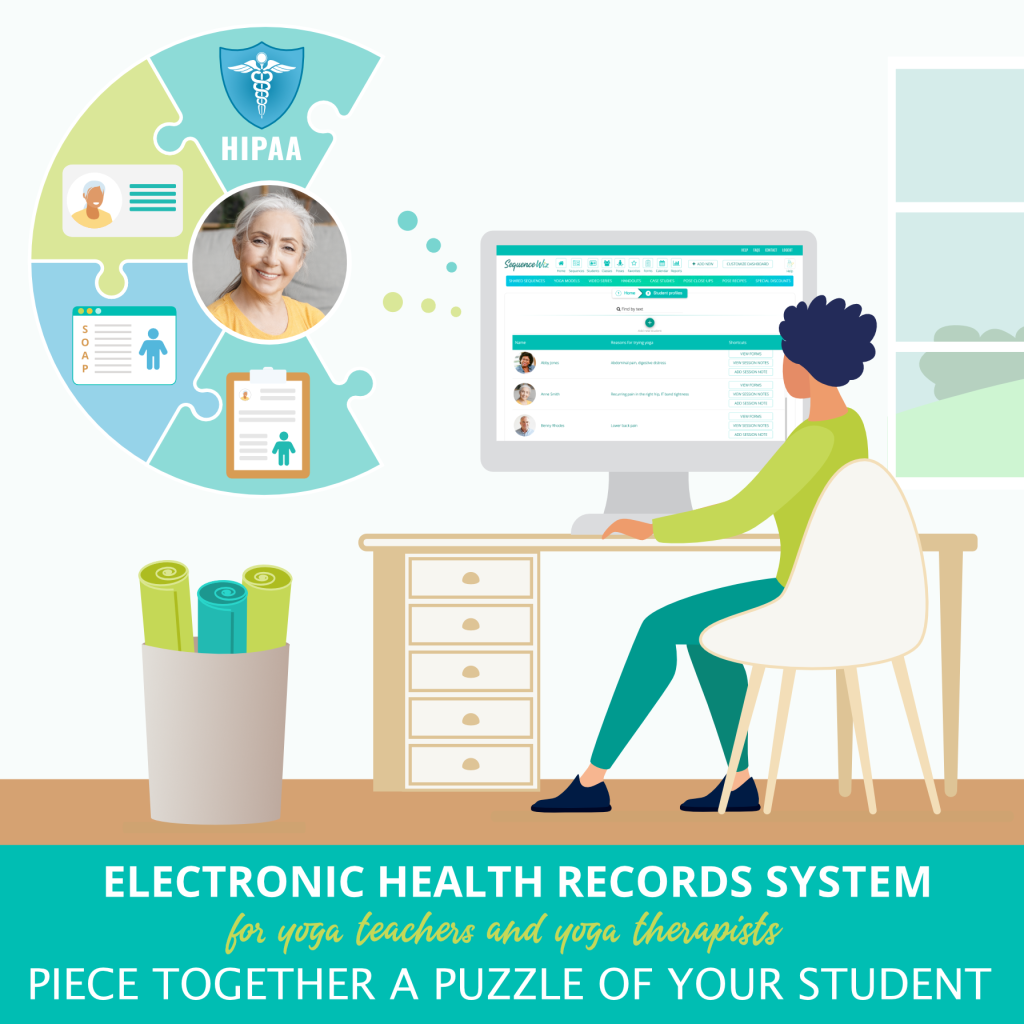
Yoga teachers and therapists also gather information about their students, including their medical history, assessments, evaluations, and goals and make session notes, lifestyle recommendations, and yoga practices.
Collect your students’ data, assess it through the yogic lens, create your plan of action, and keep track of their progress.